What is a Motherboard?
The motherboard is the main circuit board inside your PC. Every components at some point communicates through the motherboard, either by directly plugging into it or by communicating through one of the motherboards ports. The motherboard is one big communication highway. Its purpose inside your PC is to provide a platform for all the other components and peripherals to talk to each other.
Types of Motherboards
The type of motherboards depends on the CPU it was designed for. You can therefore categories motherboards by which socket type they have. e.g. Socket A, Socket 478 etc. The Type of motherboard you buy is very important, as it will need to house your CPU, and they are not interchangeable. When buying a motherboard, it will always tell you what socket type it has.When Buying a Motherboard
As everything you have on the PC at some point needs the motherboard, you need to consider these components when buying a motherboard. Foe example, if you have a lot of devices with a PCI interface that you wish to use, there is little point buying a motherboard that only offers you 3 PCI slots. Like wise with memory, you have to make sure that there are enough slots for the amount of memory you have or wish to have.The motherboard also needs the correct type of interface for your Memory, Graphics card, Hard disks and other items as well. You will find that most motherboards offer everything you need however it needs checking on when buying. Its especially important to pay detail to your motherboard if you want to use older components, which a new motherboard may or may not support.
The major difference between motherboards that support the same CPU is the model of the chipset (more on the chipset later). Different chipsets offer different performance and different features in terms of memory support, AGP port speed, Multiplier numbers, Bus speeds and much more.
Speed of a Motherboard
Motherboards have got to be one of the hardest components to measure the speed of. Performance can really only be measured by benchmarking using the same components in several motherboards of the same type. You often find that motherboards with the same chipset have roughly the same performance in real world tests. The minor differences that do occur are down to the quality of the materials used and the quality of the manufacturing.The Motherboards speeds that are quoted on the box are maximum supported speeds for other components. For example motherboards will quote the maximum FSB (Front Side Bus) speed. However without a CPU that also supports this speed, it will never be reached. Likewise when it quotes the maximum memory speed. The memory of this speed has to be present.
What is a Motherboard Chipset?
A motherboard chipset controls all the data that flows through the data channels (buses) of the motherboard. The primary function of the motherboard chipset is to direct this data to the correct area's of the motherboard, and therefore the correct components.Components of a Motherboard
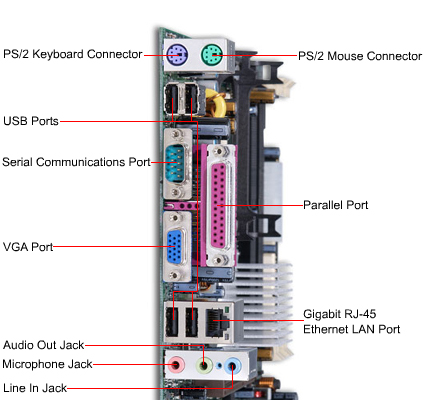
The motherboard contains many connections for all type of components. Motherboards contain expansion slots such as the ISA, PCI, AGP and DIMM sockets. It also contains external connections for your onboard sound card, USB ports, Serial and Parallel ports, PS/2 ports for your keyboard and mouse as well as network and Firewire connections.So the motherboard has a massive part to play in the workings of your PC. Components that you buy all rely on the motherboard to have the correct connections are available and working. Its best to buy a decent motherboard especially if you plan on buying extra's in the future.
by : http://www.techiwarehouse.com/cat/13/Motherboard
